Bypass the https://github.com/418sec/node-pdf-image/pull/1 Fix#2
Bypass the https://github.com/418sec/node-pdf-image/pull/1 Fix#2Mik317 wants to merge 1 commit into418sec:masterfrom
Conversation
|
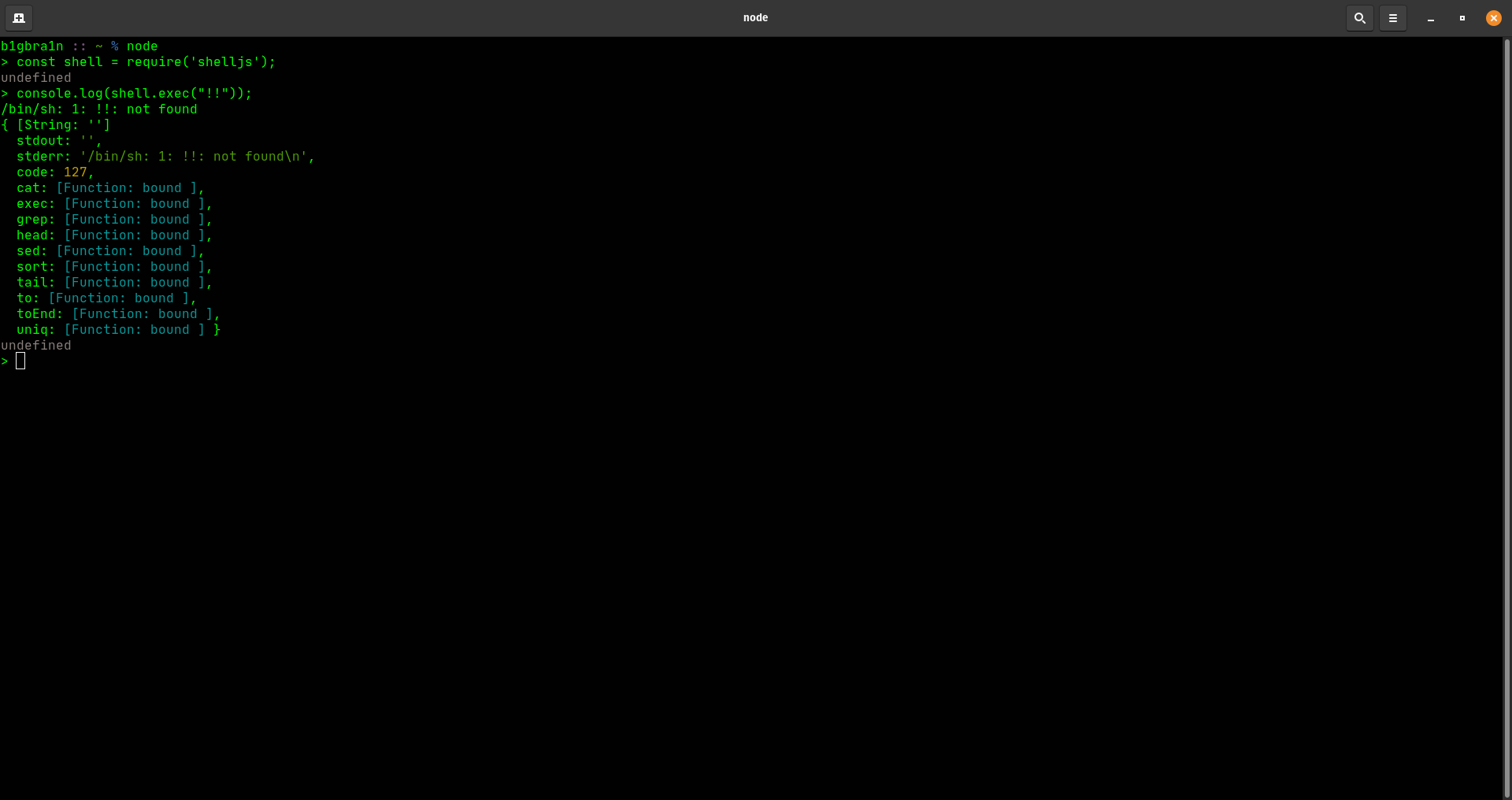
Nice Catch! It does lead to an ❓ How chaining it to RCE is not possible (or Bypassing The Fix) The For instance, I tried executing this command via Node (as this project is written in it): As you can see from the above screenshot, executing the Hence this does not bypass the fix for the RCE although it is a valid finding of an I may be wrong, so can you please demonstrate a PoC to chain Thanks & Regards, |
|
Next time, instead of posting the whole link to the other pull request, do #1. |
|
Hi @mufeedvh :), Yep, I can confirm it's not possible completely bypass your fix (good work mate ;)) $ child_process.exec('!!');
...
{ Error: Command failed: `!!`
/bin/sh: 1: !!: not found
at ChildProcess.exithandler (child_process.js:294:12)
at ChildProcess.emit (events.js:198:13)
at ChildProcess.EventEmitter.emit (domain.js:466:23)
at maybeClose (internal/child_process.js:982:16)
at Socket.stream.socket.on (internal/child_process.js:389:11)
at Socket.emit (events.js:198:13)
at Socket.EventEmitter.emit (domain.js:466:23)
at Pipe._handle.close (net.js:607:12) killed: false, code: 127, signal: null, cmd: '`!!`' }Anyway, as I outlined before, it's still possible PS: Hi @RadoiAndrei :), excuse me, I'm not so practice with Git. The next time I'll use the Regards, Mik |
 JamieSlome
left a comment
JamieSlome
left a comment
There was a problem hiding this comment.
@Mik317 - we really appreciate your contributions and spotting the argument injection! As this wasn't a bounty, we can't award it to you, but to say thank you, we will be sending some credits your way! 🍰 💰 We look forward to reviewing more of your fixes/disclosures 😉in the future!
From the huntr team
|
Sorry @Mik317, we enjoyed reviewing your fix but another was selected. We appreciate your effort and look forward to reviewing more of your fixes in the future! 🔨 😎 |
|
Hi @JamieSlome :),
? (I'm so curious lol). Hey @mufeedvh :), Regards, Mik |
Hi Huntr Dev team :),
as I had promised, I would have started working on some of yours modules.
I'd like to say that the #1 fix (which has been
verifiedas fixing the RCE vuln disclosed previously), doesn't fix the issue.The fix proposed by @mufeedvh doesn't check for the
"(double quote) character, making an attacker able to escape anyway thefilenamepassed asargument, leading toargument injection.Also, take in mind that in the
bash world, the!!(double exclamation point) can be used to refer to the last command executed in the same shell.Chaining this 2 characters, an attacker may be able still to bypass the fix, leading anyway to RCE.
I'm attaching my
pull requestwhichblacklistsalso those 2 characters, in order to avoid this (unprobable, but still fully exploitable) scenario :).Best, Mik