Conversation
|
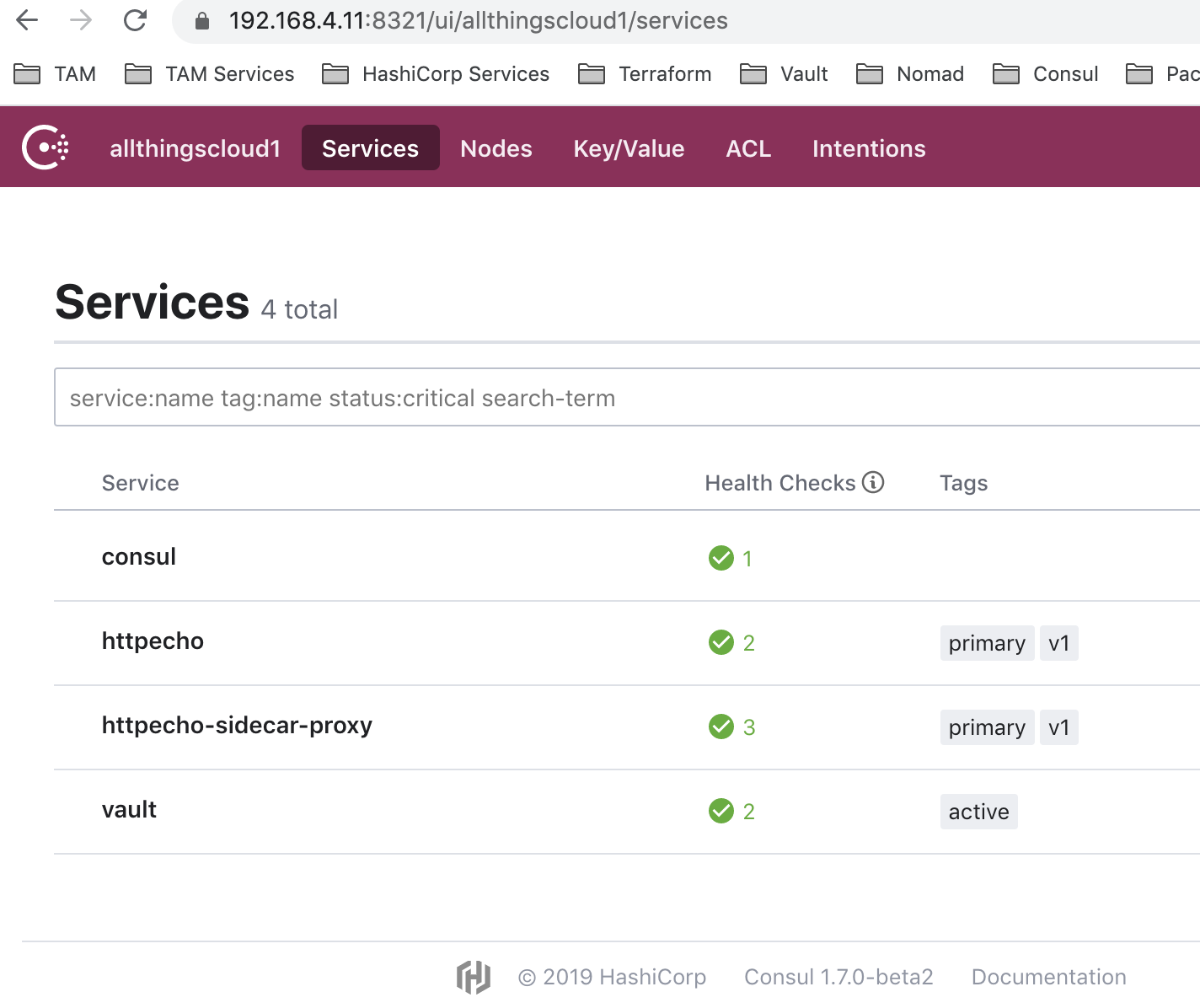
Awesome!!! Thanks for the swift response - verified that this works with my services. vagrant@app01:~$ /usr/local/bin/consul connect envoy -http-addr=https://127.0.0.1:8321 -ca-file=/usr/local/bootstrap/certificate-config/consul-ca.pem -client-cert=/usr/local/bootstrap/certificate-config/cli.pem -client-key=/usr/local/bootstrap/certificate-config/cli-key.pem -token=${SERVICETOKEN} -sidecar-for httpecho -bootstrap
{
"admin": {
"access_log_path": "/dev/null",
"address": {
"socket_address": {
"address": "127.0.0.1",
"port_value": 19000
}
}
},
"node": {
"cluster": "httpecho",
"id": "httpecho-sidecar-proxy"
},
"static_resources": {
"clusters": [
{
"name": "local_agent",
"connect_timeout": "1s",
"type": "STATIC",
"tls_context": {
"common_tls_context": {
"validation_context": {
"trusted_ca": {
"inline_string": "-----BEGIN CERTIFICATE-----\nMIIC7TCCApSgAwIBAgIRAM3rRDt+uEgHLc0aVWKJvNMwCgYIKoZIzj0EAwIwgbkx\nCzAJBgNVBAYTAlVTMQswCQYDVQQIEwJDQTEWMBQGA1UEBxMNU2FuIEZyYW5jaXNj\nbzEaMBgGA1UECRMRMTAxIFNlY29uZCBTdHJlZXQxDjAMBgNVBBETBTk0MTA1MRcw\nFQYDVQQKEw5IYXNoaUNvcnAgSW5jLjFAMD4GA1UEAxM3Q29uc3VsIEFnZW50IENB\nIDI3MzcxMzMxMjgxNTE5NTk2ODgyNDI4MjcyOTA0MDg2ODY1NDI5MTAeFw0yMDAx\nMDcxMjI1MzlaFw0yNTAxMDUxMjI1MzlaMIG5MQswCQYDVQQGEwJVUzELMAkGA1UE\nCBMCQ0ExFjAUBgNVBAcTDVNhbiBGcmFuY2lzY28xGjAYBgNVBAkTETEwMSBTZWNv\nbmQgU3RyZWV0MQ4wDAYDVQQREwU5NDEwNTEXMBUGA1UEChMOSGFzaGlDb3JwIElu\nYy4xQDA+BgNVBAMTN0NvbnN1bCBBZ2VudCBDQSAyNzM3MTMzMTI4MTUxOTU5Njg4\nMjQyODI3MjkwNDA4Njg2NTQyOTEwWTATBgcqhkjOPQIBBggqhkjOPQMBBwNCAARA\nOIKz3Ug46aNtWlib1L79zU1gNfQBqvDJjtVMlz2xf9VwB4o27luxCgG722rxEbTA\nVMBMPngop8B+9hNwmxEXo3sweTAOBgNVHQ8BAf8EBAMCAYYwDwYDVR0TAQH/BAUw\nAwEB/zApBgNVHQ4EIgQgSuKoiV//3Ldz3B9uQ6cDqH/MBSrcVHSWEgn+lnx4/IMw\nKwYDVR0jBCQwIoAgSuKoiV//3Ldz3B9uQ6cDqH/MBSrcVHSWEgn+lnx4/IMwCgYI\nKoZIzj0EAwIDRwAwRAIgFLAO59n/zQ8OmKcH8Ng71qnhbFaq0yKPvEubC5tuEsIC\nIBJT0C01RCWFJxnouBF3l3SKvrHYNCyDG4b86IoN8Wx0\n-----END CERTIFICATE-----\n"
}
}
}
},
"http2_protocol_options": {},
"hosts": [
{
"socket_address": {
"address": "127.0.0.1",
"port_value": 8502
}
}
]
}
]
},
"stats_config": {
"stats_tags": [
{
"regex": "^cluster\\.((?:([^.]+)~)?(?:[^.]+\\.)?[^.]+\\.[^.]+\\.[^.]+\\.[^.]+\\.[^.]+\\.consul\\.)",
"tag_name": "consul.custom_hash"
},
{
"regex": "^cluster\\.((?:[^.]+~)?(?:([^.]+)\\.)?[^.]+\\.[^.]+\\.[^.]+\\.[^.]+\\.[^.]+\\.consul\\.)",
"tag_name": "consul.service_subset"
},
{
"regex": "^cluster\\.((?:[^.]+~)?(?:[^.]+\\.)?([^.]+)\\.[^.]+\\.[^.]+\\.[^.]+\\.[^.]+\\.consul\\.)",
"tag_name": "consul.service"
},
{
"regex": "^cluster\\.((?:[^.]+~)?(?:[^.]+\\.)?[^.]+\\.([^.]+)\\.[^.]+\\.[^.]+\\.[^.]+\\.consul\\.)",
"tag_name": "consul.namespace"
},
{
"regex": "^cluster\\.((?:[^.]+~)?(?:[^.]+\\.)?[^.]+\\.[^.]+\\.([^.]+)\\.[^.]+\\.[^.]+\\.consul\\.)",
"tag_name": "consul.datacenter"
},
{
"regex": "^cluster\\.((?:[^.]+~)?(?:[^.]+\\.)?[^.]+\\.[^.]+\\.[^.]+\\.([^.]+)\\.[^.]+\\.consul\\.)",
"tag_name": "consul.routing_type"
},
{
"regex": "^cluster\\.((?:[^.]+~)?(?:[^.]+\\.)?[^.]+\\.[^.]+\\.[^.]+\\.[^.]+\\.([^.]+)\\.consul\\.)",
"tag_name": "consul.trust_domain"
},
{
"regex": "^cluster\\.(((?:[^.]+~)?(?:[^.]+\\.)?[^.]+\\.[^.]+\\.[^.]+)\\.[^.]+\\.[^.]+\\.consul\\.)",
"tag_name": "consul.target"
},
{
"regex": "^cluster\\.(((?:[^.]+~)?(?:[^.]+\\.)?[^.]+\\.[^.]+\\.[^.]+\\.[^.]+\\.[^.]+)\\.consul\\.)",
"tag_name": "consul.full_target"
},
{
"tag_name": "local_cluster",
"fixed_value": "httpecho"
}
],
"use_all_default_tags": true
},
"dynamic_resources": {
"lds_config": {
"ads": {}
},
"cds_config": {
"ads": {}
},
"ads_config": {
"api_type": "GRPC",
"grpc_services": {
"initial_metadata": [
{
"key": "x-consul-token",
"value": "dc612e72-e2cd-dc8c-b9d2-53315ae41258"
}
],
"envoy_grpc": {
"cluster_name": "local_agent"
}
}
}
}
}
vagrant@app01:~$ |
|
Thanks a lot @allthingsclowd! I will merge as soon as someone reviewed it. |
 banks
left a comment
banks
left a comment
There was a problem hiding this comment.
Thanks @i0rek.
I vaguely recall the change here but need to go back and understand why it was made a bit more.
I'm also a bit concerned that we managed to break something so fundamental to Connect without it being caught by integration tests at least - we certainly have an integration test that uses this command to verify it works but perhaps it doesn't currently use agent TLS?
Would be awesome if we could at least make a follow up issue to add an integration test for this although I don't want to block the fix getting out.
|
Agreed @banks, I will make a followup issue so that we don't forget to add it to the int tests. |
I didn't want to use inline_string initially, because the newlines have to be escaped. But now that seems easier than fixing the bytes representation.
Fixes #7023